TryHackMe | Masterminds Walkthrough
Practice analyzing malicious traffic using Brim.
Link-https://tryhackme.com/room/mastermindsxlq
[Infection 1]
Provide the victim’s IP address.
Load infection1.pcap in Brim
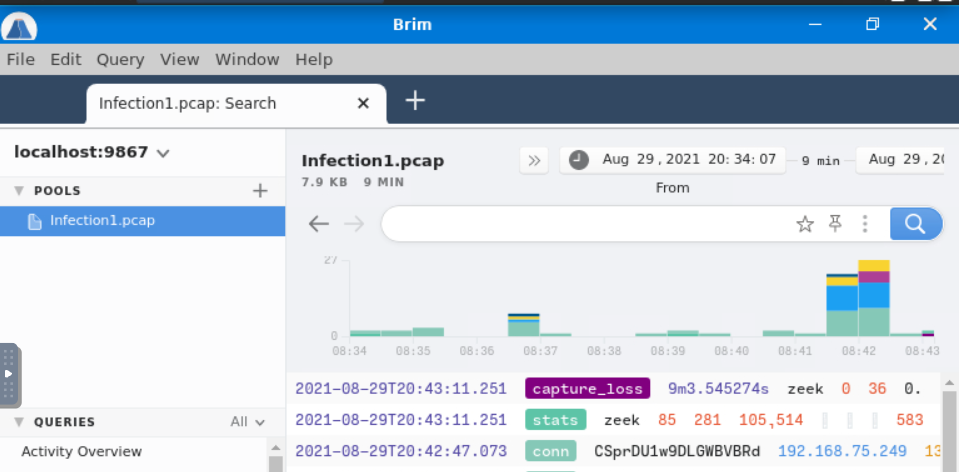
Check the source IP of “Http Requests”
192.168.75.249
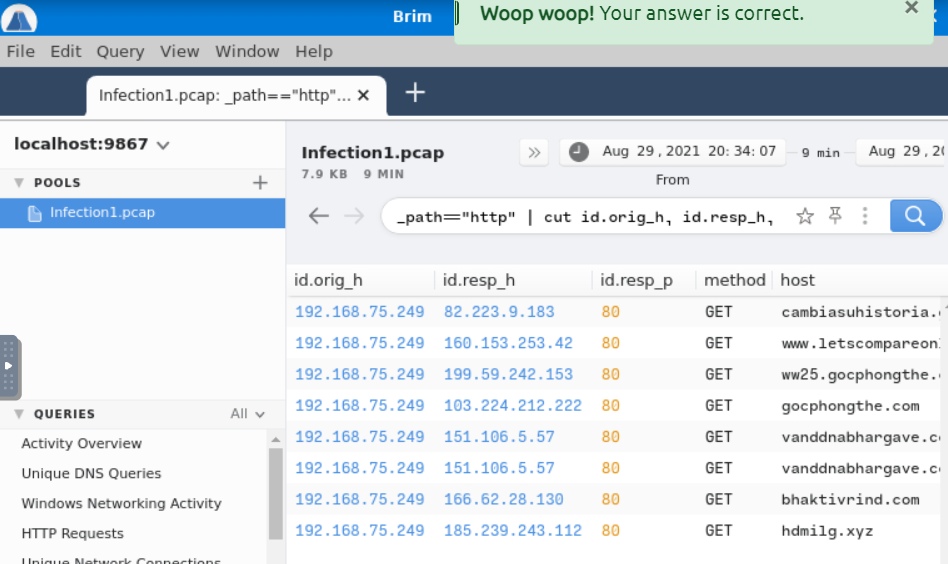
The victim attempted to make HTTP connections to two suspicious domains with the status ‘404 Not Found’. Provide the hosts/domains requested.

cambiasuhistoria.growlab.es, www.letscompareonline.com
The victim made a successful HTTP connection to one of the domains and received the response_body_len of 1,309 (uncompressed content size of the data transferred from the server). Provide the domain and the destination IP address.
Check the “Http Requests”

ww25.gocphongthe.com,199.59.242.153
How many unique DNS requests were made to cab[.]myfkn[.]com domain (including the capitalized domain)?
Check “Unique DNS Queries”
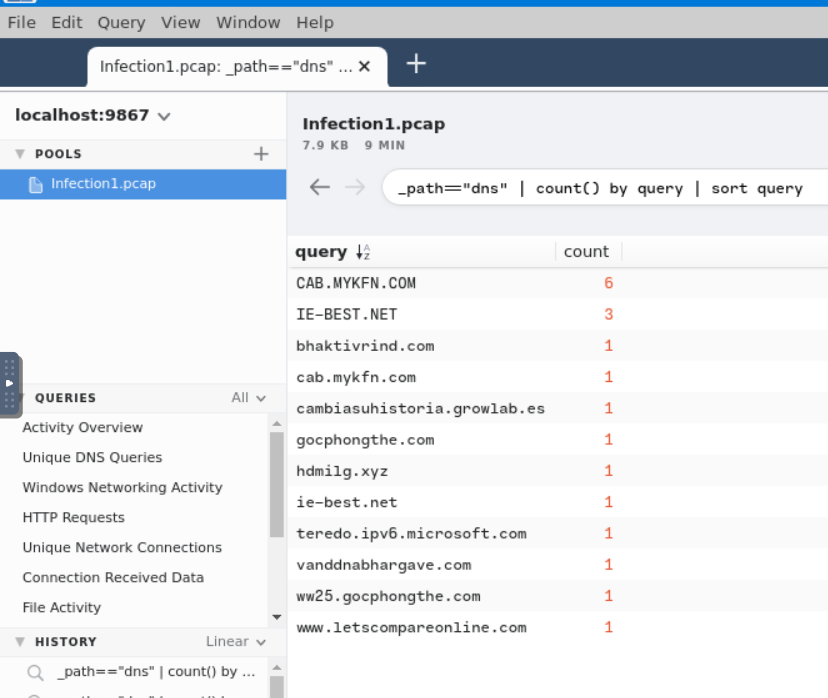
7
Provide the URI of the domain bhaktivrind[.]com that the victim reached out over HTTP.
Check the “Http Requests”
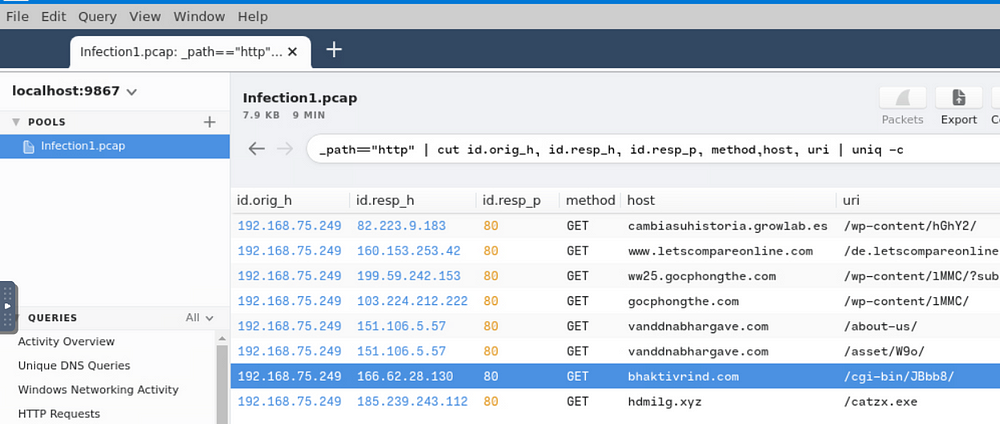
/cgi-bin/JBbb8/
Provide the IP address of the malicious server and the executable that the victim downloaded from the server.
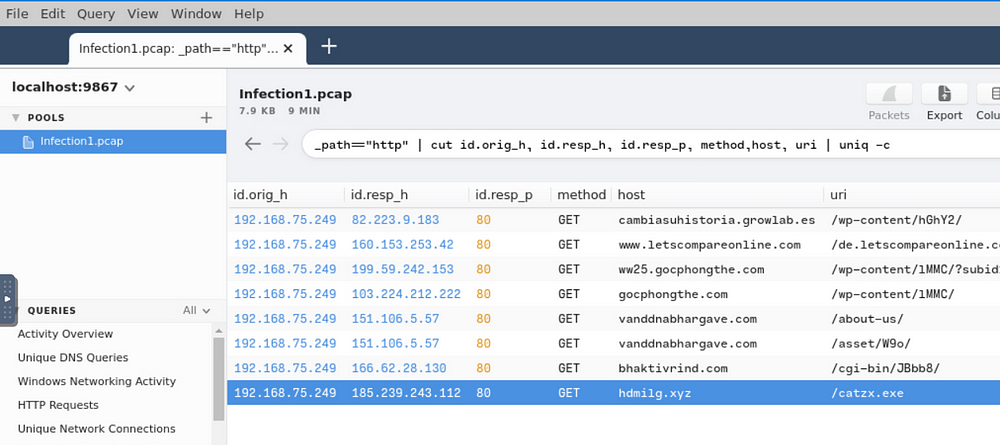
185.239.243.112,catzx.exe
Based on the information gathered from the second question, provide the name of the malware using VirusTotal.
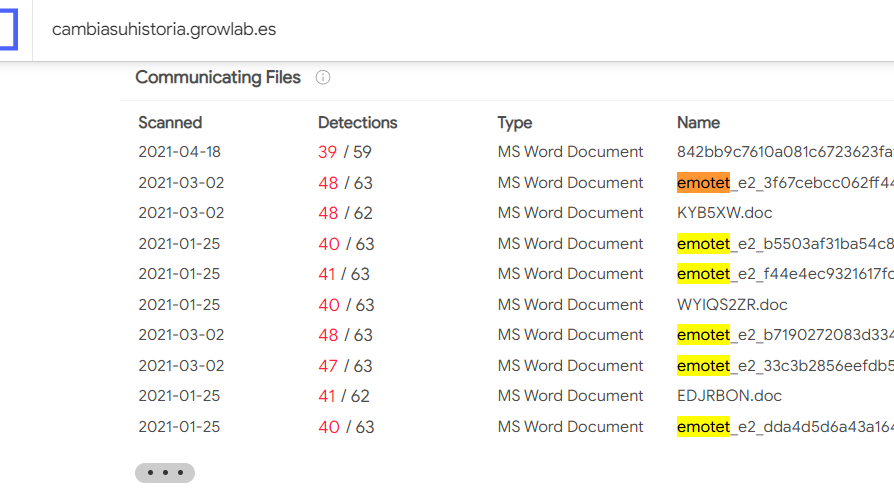
Emotet
[Infection 2]
Provide the IP address of the victim machine.
Load infection2.pcap in Brim
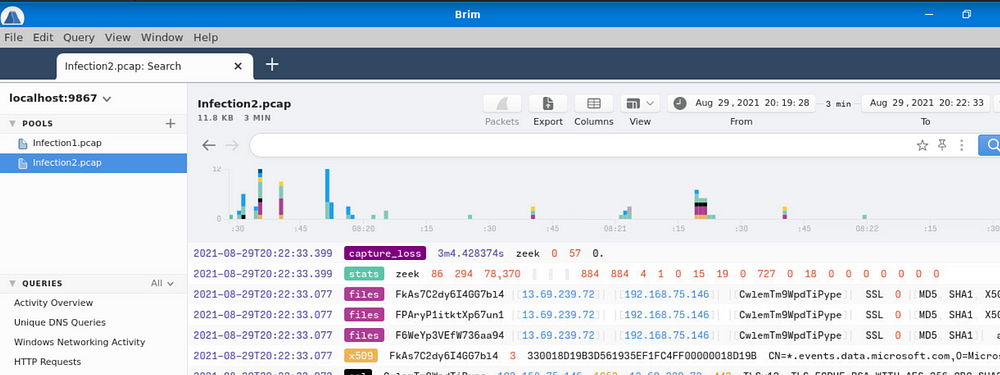
Check the source IP of “Http Requests”
192.168.75.146
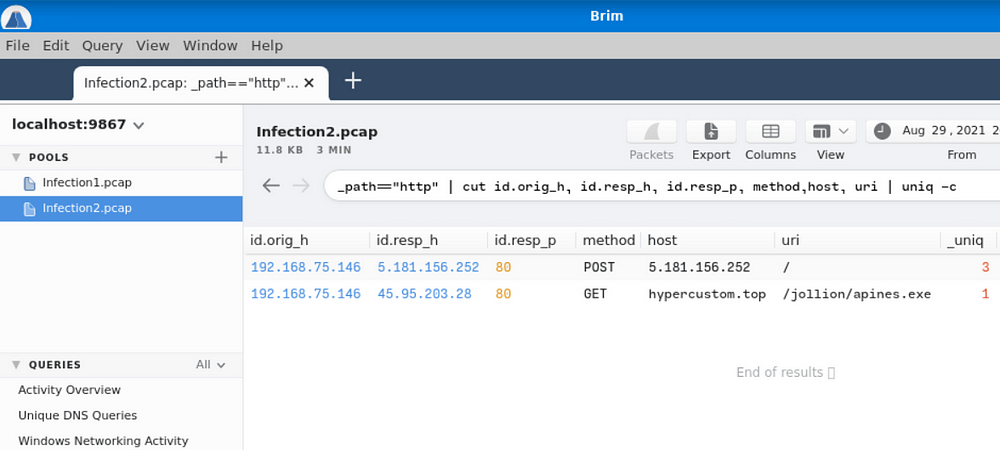
Provide the IP address the victim made the POST connections to.
5.181.156.252
How many POST connections were made to the IP address in the previous question?
3
Provide the domain where the binary was downloaded from.
hypercustom.top
Provide the name of the binary including the full URI.
/jollion/apines.exe
Provide the IP address of the domain that hosts the binary.
45.95.203.28
There were 2 Suricata “A Network Trojan was detected” alerts. What were the source and destination IP addresses?
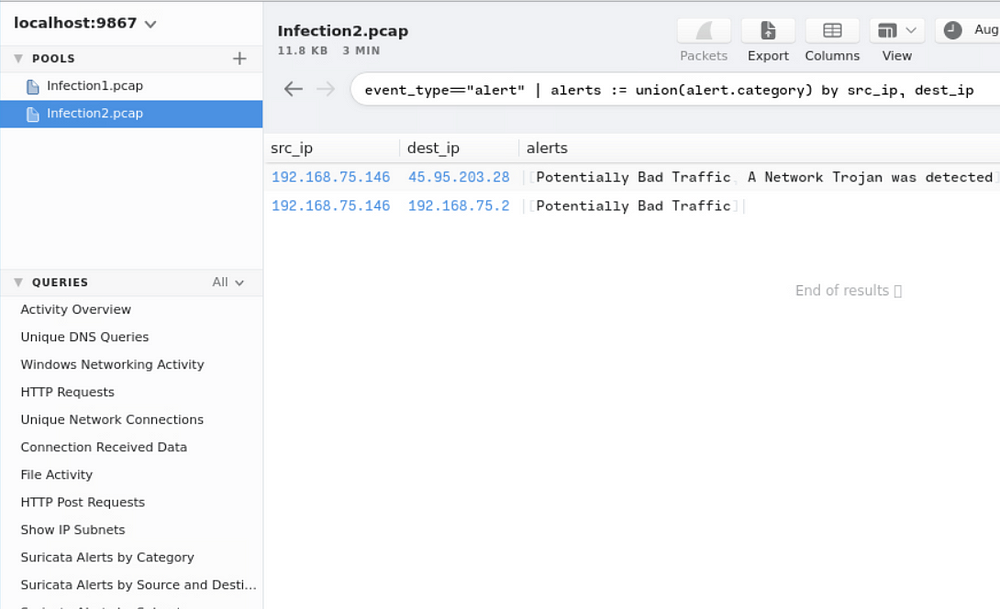
192.168.75.146,45.95.203.28
Taking a look at .top domain in HTTP requests, provide the name of the stealer (Trojan that gathers information from a system) involved in this packet capture using URLhaus Database.
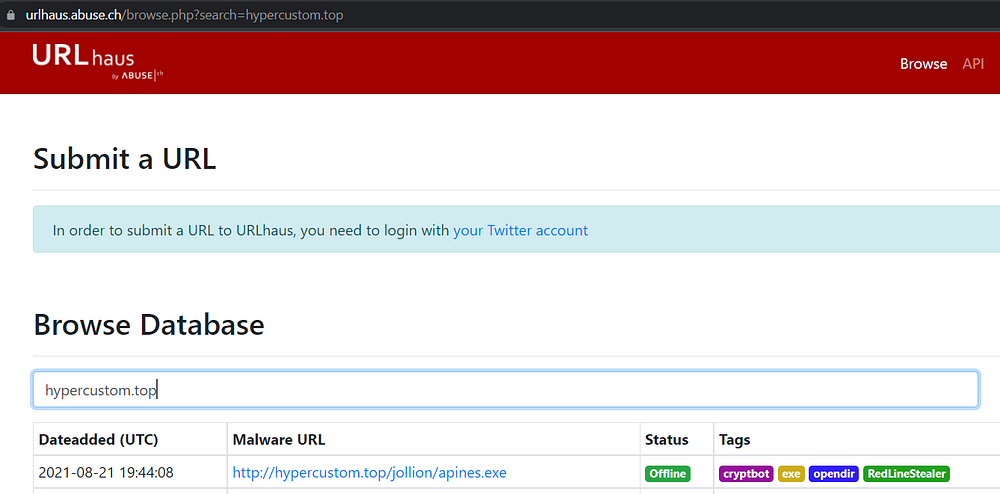
Redline Stealer
[Infection 3]
Provide the IP address of the victim machine.
Load infection3.pcap in Brim
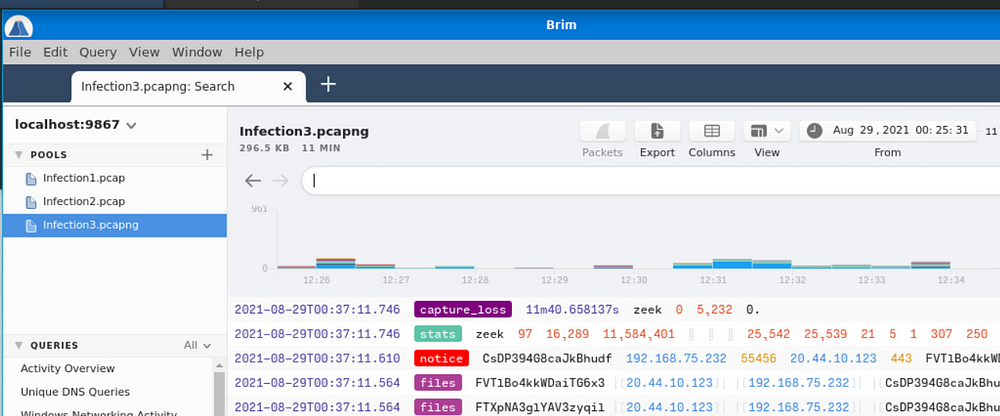
Check the source IP of “Http Requests”

192.168.75.232
Provide three C2 domains from which the binaries were downloaded (starting from the earliest to the latest in the timestamp)
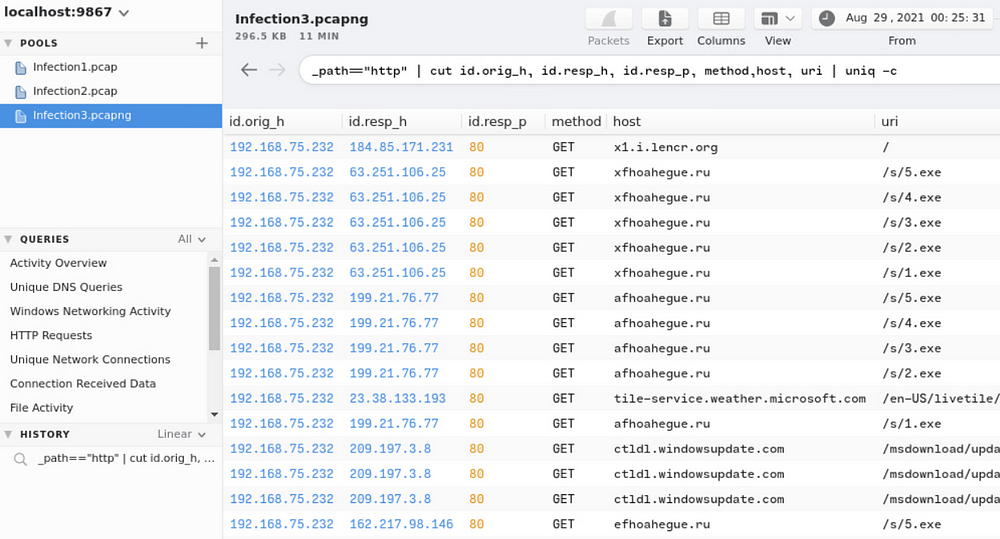
efhoahegue.ru,afhoahegue.ru,xfhoahegue.ru
Provide the IP addresses for all three domains in the previous question.
162.217.98.146,199.21.76.77,63.251.106.25
How many unique DNS queries were made to the domain associated from the first IP address from the previous answer?

2
How many binaries were downloaded from the above domain in total?
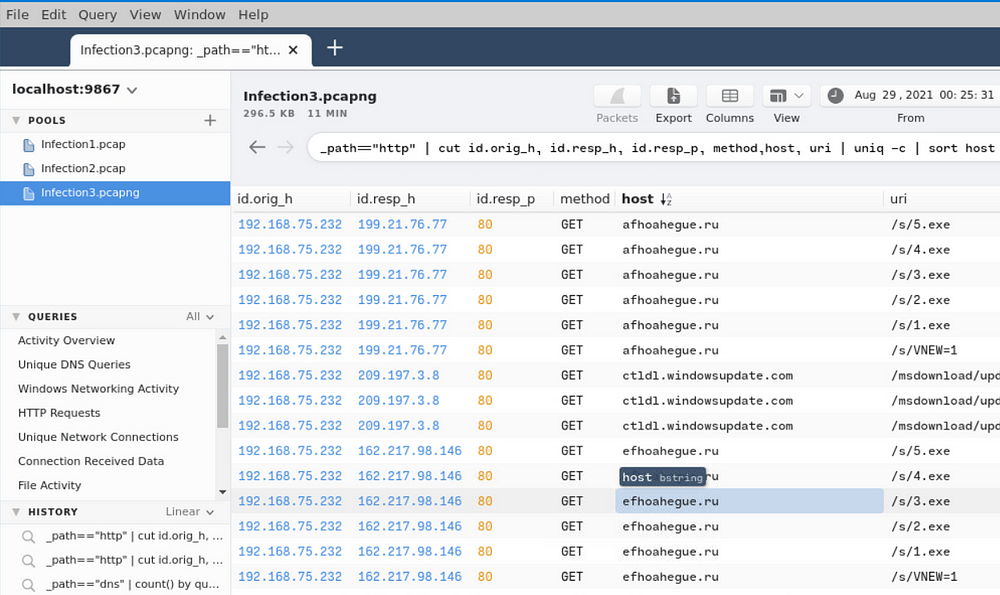
5
Provided the user-agent listed to download the binaries.
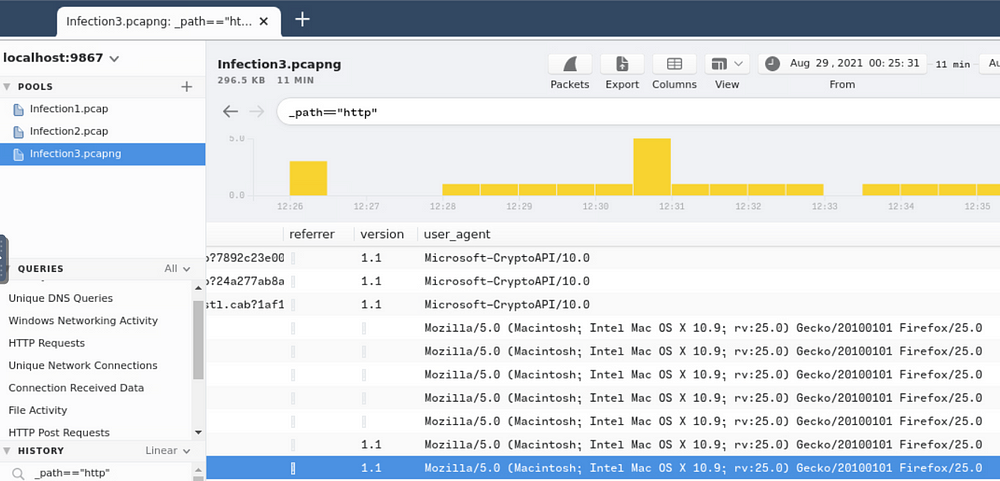
Mozilla/5.0 (Macintosh; Intel Mac OS X 10.9; rv:25.0) Gecko/20100101 Firefox/25.0
Provide the amount of DNS connections made in total for this packet capture.
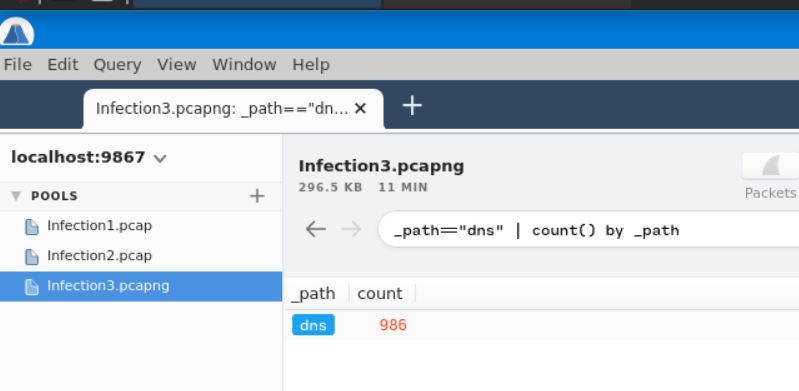
986
With some OSINT skills, provide the name of the worm using the first domain you have managed to collect from Question 2. (Please use quotation marks for Google searches, don’t use .ru in your search, and DO NOT interact with the domain directly).
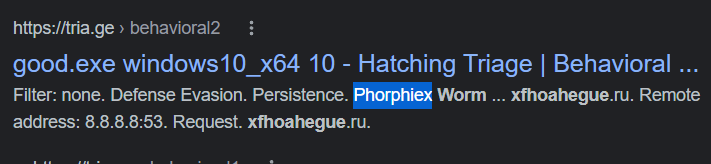
Phorphiex
That’s it! See you in the next Room :)
Comments
Post a Comment